Amazon.com: MikroTik hAP AC RouterBoard, Triple Chain Access Point 802.11ac (RB962UiGS-5HacT2HnT-US) : Electronics
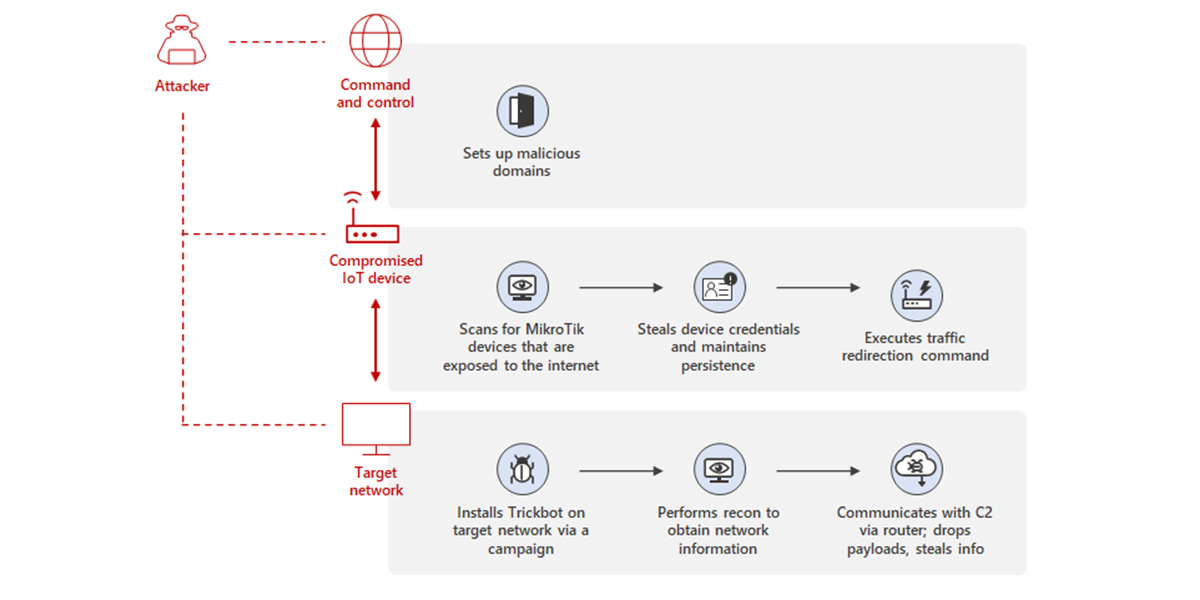
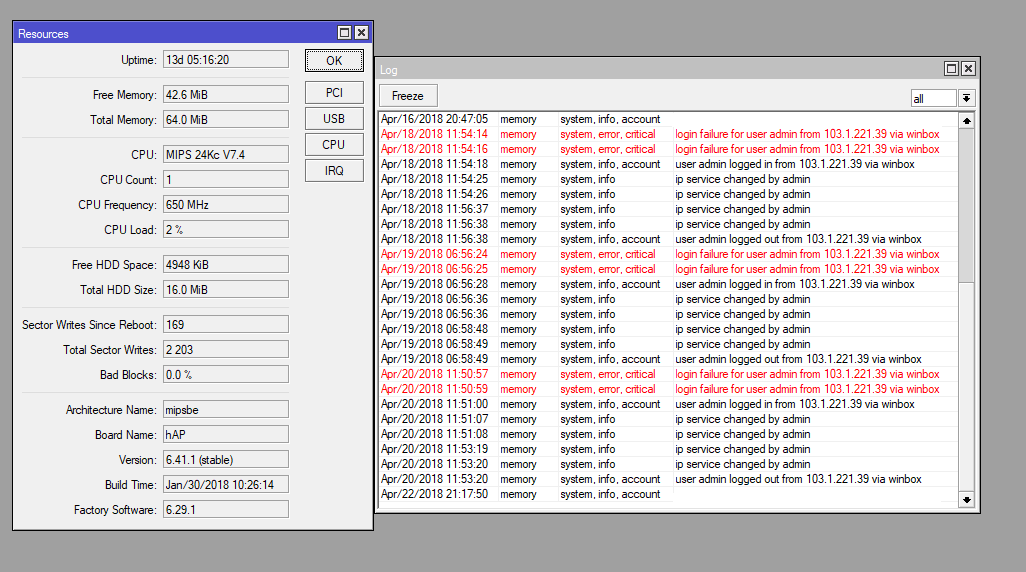
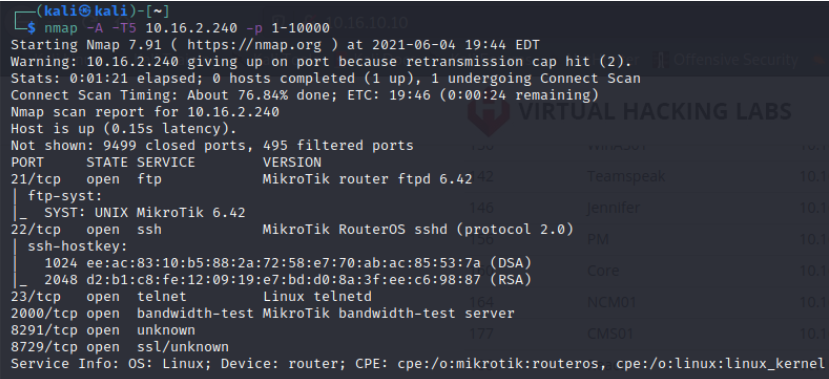
Uncovering Trickbot's use of IoT devices in command-and-control infrastructure | Microsoft Security Blog
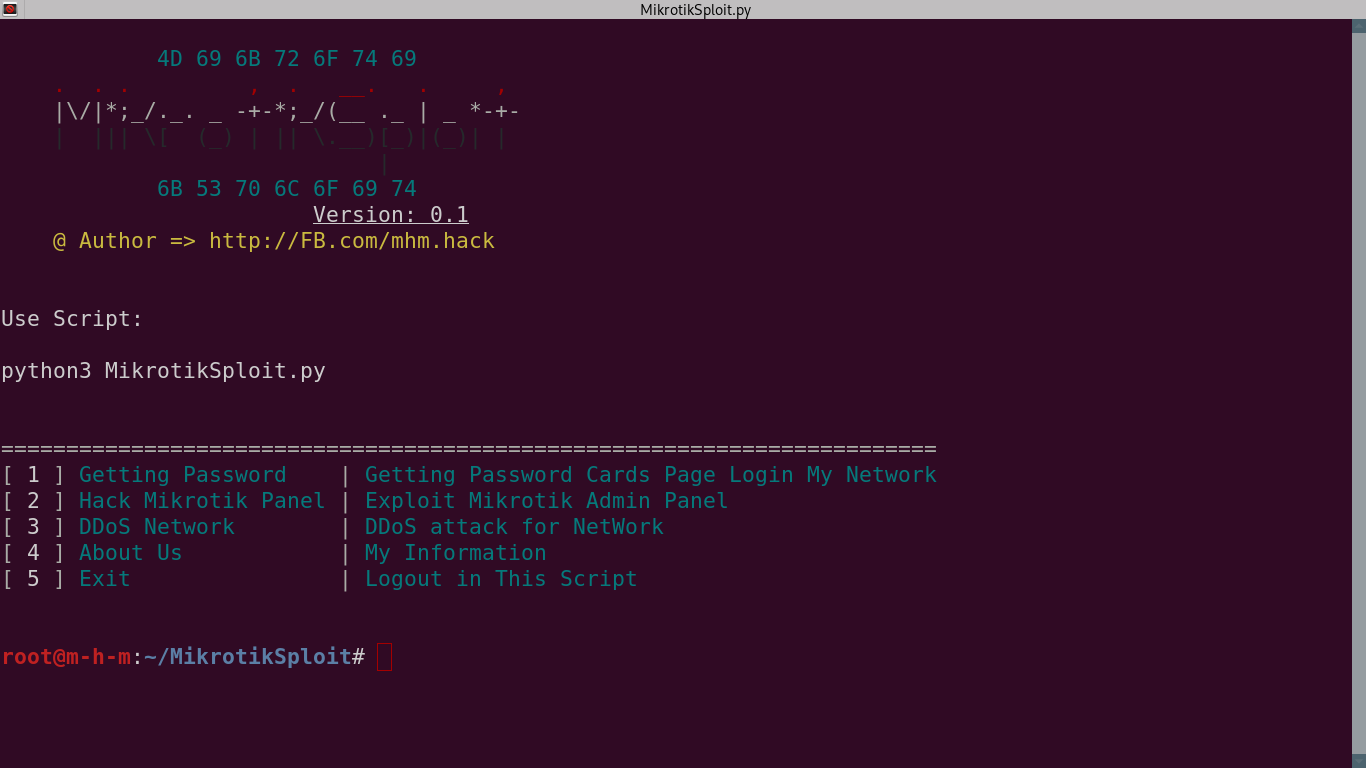
GitHub - 0x802/MikrotikSploit: MikrotikSploit is a script that searches for and exploits Mikrotik network vulnerabilities



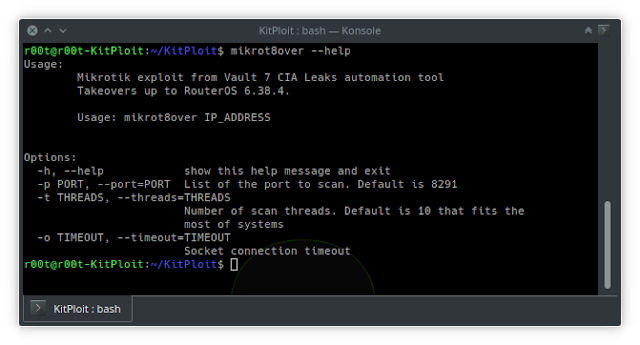












![New Tool] MKBrutus The Mikrotik RouterOS Bruteforce attacker tool v1.0.0 released – ToolsWatch.org New Tool] MKBrutus The Mikrotik RouterOS Bruteforce attacker tool v1.0.0 released – ToolsWatch.org](http://seguridadetica.files.wordpress.com/2013/11/mkbrutus_2.png)